Cybersecurity Challenges in the New Energy Era
- Hacker threats continue to prevail, with OT becoming prime targets for cybercriminals.
- In the next five years, cybersecurity will account for more than 40% of OT/industrial control transformation.
- Zombie viruses continue to expand alongside the Internet of Things. System paralysis caused by DDoS attacks will result in significant losses for owners.
- OT cybersecurity responsibilities are gradually shifting to Chief Information Security Officers (CISOs), and the importance of cybersecurity levels is
- A sheer number of event logs are created daily, but no adequate tools are available to identify key issues.
- Throughout 2023, cybersecurity and cloud technologies became increasingly intertwined, revealing a growing relationship of interdependence.
- Government, military, and IT service providers are the primary targets of hacking.
Creating a Secure Environment
Providing cybersecurity consulting services for organizations on achieving compliance with IEC 62443-3-3 or IEC 62443-2-4 and offering reports and recommendations to help them enhance system security, thus reducing production downtime and operational interruptions resulting from security incidents.

Next-Generation Firewalls
Deploying the world's most widely distributed network firewall and providing AI-driven security protection to enable rapid detection and response to known and unknown threats, thereby safeguarding networks, devices, and data, assisting crucial industrial networks in defending against cyber threats.

SD-WAN
A virtual WAN structure enables enterprises to flexibly utilize various transmission combinations, improving the traditional WAN structure's latency and application performance degradation caused by data returning to data centers. It also enhances enterprise WAN flexibility and reduces IT costs.
Flexible SIEM Architecture
Using automated identity recognition and correlated analysis of networking positions to collect and analyze diverse information sources, including logs, performance indicators, traffic, SNMP/TRAPS, APIs, security alerts, and device configuration changes. Integrating and consolidating previously independent Security Operations Center (SOC) and Network Operations Centre (NOC) to reduce excessive event information and enhance crisis resolution efficiency.

Deception Technology
Effectively expanding defense across multiple attack surfaces through diverse traps and decoys, recording and analyzing hackers’ attack methods, and integrating with firewalls or SIEM for real-time automatic isolation and prevention of attack incidents.

Industrial Network Security Standard IEC 62443
The International Electrotechnical Commission (IEC) developed the IEC 62443 standard, specifically referencing ISA 99 for industrial control security. Subsequently, ISA 99 was renamed ISA/IEC 62443. The goal is to ensure secure operation for Industrial Automation and Control Systems (IACS) from design through implementation and management. To achieve this objective, this series of standards establishes guidelines for component manufacturers, system integrators, and operators to adhere to from various perspectives. IEC 62443 stands as the only globally applicable industrial control network security standard across industries. It has been adopted by numerous sectors, aiding in the creation of more secure OT environments.
Certification
ORing's Cyber-Hardened Ethernet Switch series have achieved IEC 62443-4-2 certification, providing enhanced security and reducing the risk of cyber incidents in critical sectors such as power generation, transportation, and manufacturing.
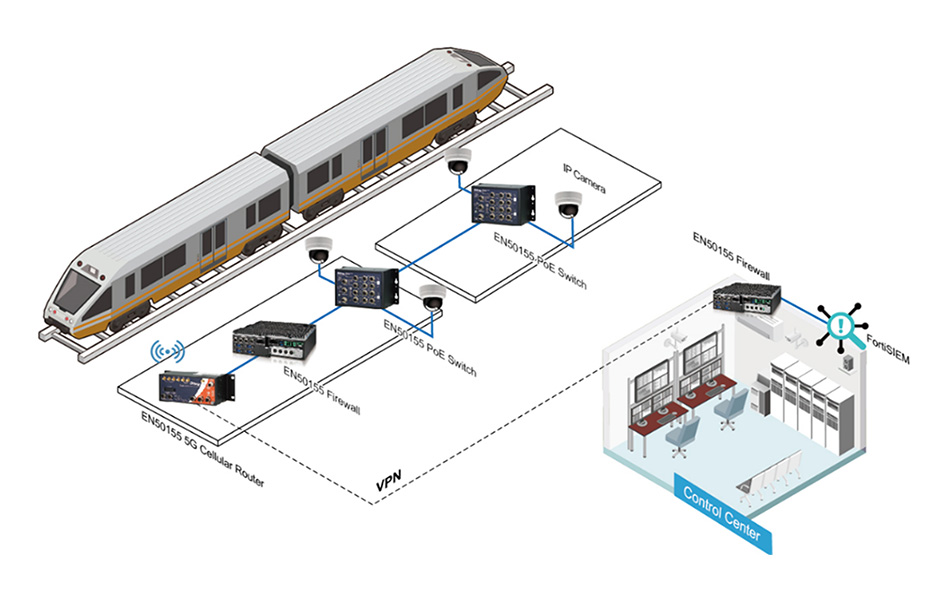
Cybersecurity for Railway Applications
Train communication systems and onboard equipment fall within the realm of Operational Technology (OT). Operational status and data are transmitted to remote traffic control centers. If these systems suffer network attacks, it can result in information loss, data misplacement, disconnection from the control center, or even critical situations such as train malfunctions.
Cybersecurity for Energy Storage Cabinets
ORing's managed cybersecurity switches are tailored to meet the requirements of substation automation systems (IEC 61850-3, IEEE 1613). The modular design supports up to 28 Gigabit ports, featuring 4 module slots and 2 power module slots (24~48VDC, 88~300VAC/VDC), ensuring application flexibility. They are aimed to meet evolving network needs, enhance communication reliability, and reduce wiring costs. The RGS-P(R)9000 series managed cybersecurity switches operate within a rated temperature range of -40 to 75°C, ensuring durability and suitability for harsh industrial environments. These switches can be easily installed in racks/DIN rails or junction boxes, providing comprehensive OT protection while maintaining stable communication.
.jpg)
Cybersecurity Power Plants
Research indicates that over 130,000 solar power generation monitoring systems are exposed on public networks, highlighting deficiencies in cyber hygiene. Stringent access control and cybersecurity measures should be implemented to prevent reduced energy production, system instability, or theft of administrator credentials due to attacks.
.jpg)
Cybersecurity for EV Charging Stations
At EV charging stations, ORing’s managed switches support functions like login permissions, Device Binding, and DHCP Snooping to enhance security. Using Open-Vision Pro for centralized management and device parameter settings, it collects diverse information and records from various security and network devices across brands at remote control centers. It also implements next-generation firewalls, offering high-level security protection and in-depth visualization to counter network threats.
.jpg)
Cybersecurity for New Energy Systems
ORing’s solution integrates FortiGate VM firewall, Open-Vision Pro 5.0, and its own-branded networking products. Leveraging Open-Vision Pro 5.0 to parse Syslog data collected from FortiGate, it issues commands to block network threat sources, enabling comprehensive collaborative cybersecurity measures.
.jpg)
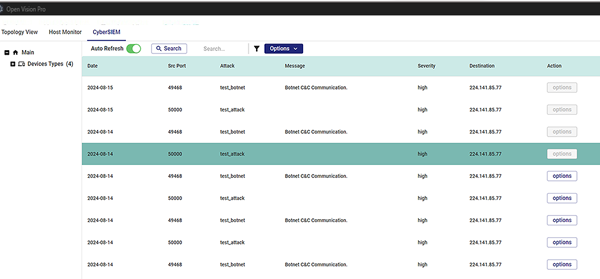
Open-Vision Pro
Open-Vision Pro 5.0 is a powerful system designed to assist network administrators in monitoring, managing, and maintaining their network devices. It also integrates cybersecurity firewalls with ORing's networking devices, including network switches, wireless access points, routers, and other products. This integration establishes a comprehensive OT cybersecurity collaborative system, supporting rapid intrusion detection and isolation. It enables intelligent automatic activation of collaborative defense and protection across devices and network segments.
Industrial OT Cybersecurity Solution

IGS-P9084GPMI
- DIN-rail L2 Ethernet Switch
- IEC 61850-3 & IEEE 1613 certificated
- 8GbE + 4 SFP ports + 1 slot
- With optional FortiGate VM module

RGS-P(R)9000 series
- Rackmount L2/L3 Ethernet Swtich
- IEC 61850-3 & IEEE 1613 certificated
- 4 slots
- With optional FortiGate VM module

IGPS-9084GP-LA
- 8 10/100/1000 PSE, 802.3at
- 4 1G SFP sockets
- Developed according to IEC 62443-4-1 and compliant with IEC 62443-4-2

IGS-9084GP-LA
- 8 10/100/1000 RJ45
- 4 1G SFP sockets
- Developed according to IEC 62443-4-1 and compliant with IEC 62443-4-2
